Some incorporate in Panama, Seychelles, etc.
Mostly I am using NordVPN. They even offer Onion over VPN services (which I don’t use).
Mostly I am setting up a Seychelles or Panama server on my VPN router (just in case).
I found a user review about them online. Please find it below:
### Located in Panama (Safe Jurisdiction, No Data Retention Law)
According to their website (link removed by moderator @0brand), NordVPN was launched 2008 in Panama and is operated by Tefincom co S.A.
For some, this can raise a red flag.
However, that’s common practice.
All (link removed by moderator @0brand) are located in independent countries that don’t share information on logging (Switzerland, Singapore, Caymans, British Virgin Islands and so on).
NordVPN definitely hides this information well enough. And it’s good for their users, too.
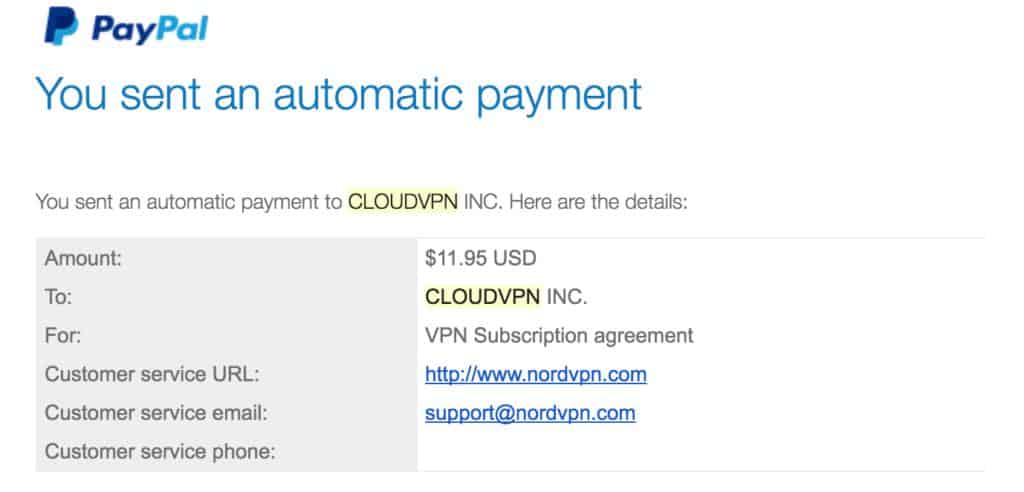
However, when I actually paid for the test account to write this NordVPN review, my payment went to CloudVPN Inc (located in the US). So aren’t they really located in Panama like the claim?
To find out, I contacted NordVPN directly and here’s what they wrote to me:
> “Hi Brad,
>
>
>
> First, NordVPN and all the infrastructure we use is being run by Tefincom S.A. and operates under the jurisdiction of Panama.
>
>
>
> CloudVPN is used only as a payment collector in order to improve the acceptance rate, as banks are suspicious towards transactions made to Panama and tend to complicate or terminate such payments. It’s a simple and common practice.
>
>
>
> Our company has absolutely nothing to do with the service itself in the legal or any other matters.”
To be honest – this makes a lot of sense. They are “officially” based in Panama which helps them to avoid any data retention laws.
I don’t know what to think about it. Any advice?
Please don’t post links for advertisements. (@0brand moderator)