Maybe then you can categorize them, each group into specific title.
Weak opinion: I would guess that most users are only/mostly interested in hosting providers that fulfill as much as possible of your criteria. Only crypto support is not very interesting and might even be a distraction. Unless, you like to list them for the purpose of others not loosing time with providers that support crypto but fail at other criteria. The first post can probably just be an introduction text and link to our mediawiki.
In any case, as you prefer.
This plan requires more time due to redundant entries across multiple countries on the Tor Project’s Good Bad ISPs page, which means it requires overhauling its primary sorting method to individual web hosting providers instead, among other column changes. Here is an example entry with my planned contributions (subject to further revisions):
| Company/ISP | ASN | Location(s) | Bandwidth | DDoS Protection | IPv6 | ToS/AUP | Bridges | Guard/Middle | Exit | Payment Method(s) | KYC/AML | Comments | Last Updated | Consensus Weight |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Hetzner | AS24940 | Germany, Finland, Singapore, US | 1 Gbps unmetered on dedicated servers | Yes | Yes (/64) | ToC | Yes | Yes | No | Credit card, SEPA, bank/wire transfer, PayPal, and UnionPay | Yes (passport) | 05/2025 | 11.68% |
Current workload suggests this task will be completed in two months, so I will link a merge request from the Tor Project’s GitLab repository for the next monthly update.
IncogNET is no longer blocking the Tor Browser from accessing its website, so it has been added to the wiki. Cockbox and Ukrainian Data Network remain unverified due to lack of servers and/or “contact-walls”, but otherwise all entries from this topic and KYCNOT.ME have been thoroughly verified. Any web hosting providers with cryptocurrency payment support failing to meet the criteria established on the wiki have been (re)added to this topic’s wiki post instead.
I have decided to abandon the plan to completely revise the Tor Project’s Good Bad ISPs page, instead simply fetching any eligible entries from there to the Whonix Wiki for a lighter workload. Additionally, I will be editing this post throughout the month as I continue to filter each entry.
Flawed
A1[1]
Alwyzon[2]
Bthoster[2:1]
Creanova[2:2]
Digicube/Nexylan[3]
Gandi[4]
Gcore[5]
Infomaniak[2:3]
M247[3:1]
MAXKO Hosting[4:1]
OneProvider[2:4]
OVHcloud[2:5]
RackNation[2:6]
Scaleway[2:7]
Servarica[2:8]
TekSavvy[6][1:1]
T-Mobile[1:2]
Videotron[1:3]
VTR[6:1]
KYCNot.me has updated their database to include unverified community-contributed entries, but I plan on reviewing them next month. Ukrainian Data Network is currently inaccessible at the moment.
I am tackling KYCNOT.me’s hosting and VPS entries against our strict criteria on the Whonix Wiki, starting with their verified and approved services. SporeStack, one of the listed VPS services, references this website on their pricing page under the “Where else can you host for Bitcoin or Monero?” header:
This new resource along with the Tor Project’s Good Bad ISPs and KYCNOT.me’s entries will eventually be aggregated and crawled monthly, so here is a tenative roadmap to lead to that state:
- Filtering through every community contributed hosting and VPS service on
KYCNOT.me, ignoring previously crawled entries. - Filtering through the list of entries on
bitcoin-vps.com, ignoring previously crawled entries. - Filtering through the list of entries on the Tor Project’s Good Bad ISPs page, ignoring previously crawled entries.
- Aggregate and crawl all aforementioned third-party sources’ new entries every month, ignoring previously crawled entries.
The reasoning behind ignoring previously crawled entries is mostly based on efficiency, just like DNS caching, but I also have an assumption that any service provider caving in to external KYC/AML pressure is unlikely to change their privacy and/or anonymity posture to solely benefit their customer base in the future. To facilitate the last step of the roadmap, I will be utilizing the Wayback Machine to create a monthly snapshot of the bitcoin-vps.com website, since the other third-party sources have a changelog implemented for their entries in some form or another.
Seems to be going really well so far! ![]()
One small thing for the future. (Nothing went wrong yet but I should have mentioned this earlier perhaps.)
- Anonymous edit: diff
- Hosting Location Hidden Services - Wiki History
Could you please have a look at the wiki history to make sure no unknown edits slip through?
No rush at all. This can be done as per your usual schedule. As long as the edit isn’t confirmed, it’s non-public. (Only visible after login with a free account through diff or history.)
I am only mentioning this to avoid anonymous edits getting live without review.
Yes, I re-edited over the anonymous commit by correcting LNVPS’ requirements to include an SSH key. The checkout process uses its own API to generate a QR code for either the Bitcoin or Lightning invoice (alongside the wallet address), so there is no third-party payment gateway dependency whatsoever.
This stub task is now complete pending acceptance of the PrivateAlps wiki edit submission. I have also confirmed that HammerVM (https://hammervm.com/) and Strike (https://strike.bz/) request finer locale information other than country (address, city and postal code), so I have dismissed them based on this unnecessary personal information harvesting practice. If there is any issue about this decision, then such reconsideration demands that each of them will have three additional requirement entries due to the locale information mentioned earlier, along with previously crawled hosting providers being recrawled again.
The Wayback Machine is not successfully saving any snapshots of the website (regardless of reporting the issue upstream), so I manually save it (Ctrl + S) whenever I update the Whonix Wiki instead. The last update on the bitcoin-vps.com website as of this writing was March 9th.
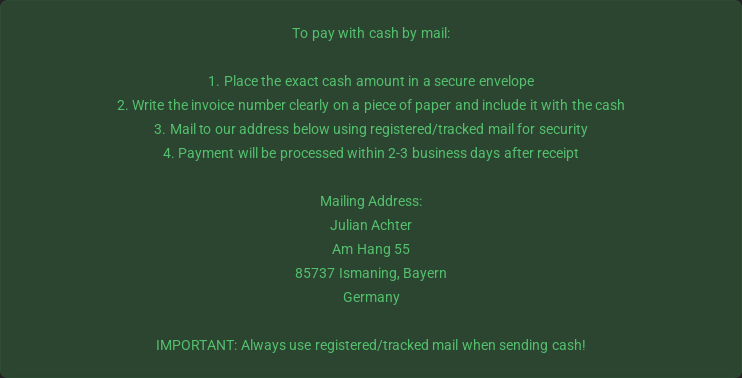
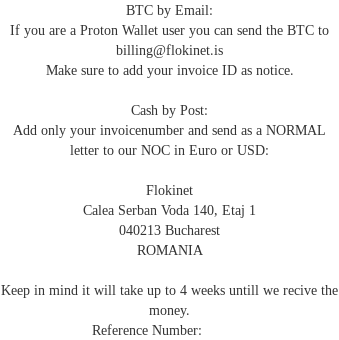
I will be finishing this task by Monday, but encountered a few hosting providers that accepts cash payment (and use Heleket or other third-party cryptocurrency payment processors):
Are either of these specific payment method instructions suggested by each hosting providers anonymous for the client or not?
The last update on the bitcoin-vps.com website as of this writing was March 18th.
This task is done pending acceptance of the remaining hosting providers from KYCNOT.me and a monthly refresh of the existing entries. Assuming there is no further discussion and/or issues about this decision, I will be treating cash payment as an anonymous payment method for the purposes of this list, even though cash carries its own set of anonymity challenges. I have also been contributing to KYCNOT.me itself too using various methods (including Codeberg), although none of them have been accepted yet.
No additional updates to the bitcoin-vps.com website since March 18th as of this writing.
I don’t disagree with the idea personally, but should the post’s title change to “List of Hosting Providers That Accept Anonymous Payment (cryptocurrency, cash, etc.)” if this is done?
Yes, I do not have @trust_level_3 or higher privileges on the Whonix Forum, so I will reflect the topic name change on the respective Whonix Wiki page after the topic title has been changed first by someone else with the required privileges.
The respective Whonix Wiki page has been updated to reflect the new topic title on the Whonix Forum, currently pending approval. Other than progression to step #2 of the roadmap, I have opened an issue to the KYC Not project on Codeberg:
Assuming a FOSS license is eventually provided, here is a roadmap detour:
- Fork the repository.
- Remove the entire pyworker directory, which uses an OpenAI API key to analyze user-submitted data.
- Self-host and maintain a separate KYC Not instance using the aforementioned Whonix Wiki page as a resource.
I can then use this separate KYC Not instance for a more comprehensive, granular analysis of each hosting provider. Here is the tenative workflow starting from step #4 of the roadmap:
- Accept only changes from me to the self-hosted KYC Not instance.
- Backport any changes to the main KYC Not instance.
- Backport any changes to the Whonix Wiki page.
The last update on the bitcoin-vps.com website as of this writing was March 24th.
Wiki edit is now accepted, post title is updated to match.
Or, alternatively, Whonix wiki could just link to your website.
Okay, I will need to make multiple changes to the KYC Not codebase:
- Categories/Types:
- Add Colocation
- Add Dedicated servers
- Add DNS
- Add Managed hosting
- Add Onion webspace
- Remove everything else except (Shared) Hosting, VPN and (VDS/)VPS
- Verification:
- Remove Community
- Networks:
- Add Yggdrasil (IncogNET).
- Currencies:
- Add multiple cryptocurrencies, including their respective tickers.
- Attributes:
- Add Non-functional Onion-Location/Onion URLs (FlokiNET and SnowCore).
- Remove “Can’t analyse ToS” due to non-usage of OpenAI.
- Remove all other attributes intended for non-hosting services.
The scoring system will need to be significantly adjusted or outright removed due to these changes. Once I have a drop-in replacement, I will follow up with a status update post in this topic.
Hi,
https://darkvps.pro accept crypto payment. NO KYC. Operate own Servers.
Okay, here are the requirements from DarkVPS:
- Email address
- JavaScript
Self-hosted BTCPay instance supporting Bitcoin and Monero with its own Onion-Location, but the main website does not have its own Onion-Location. In addition, only lists four supported operating systems, of which two are obsolete:
- Debian 12 (superceded by 13)
- Ubuntu 24.04 LTS
- AlmaLinux 9 (superceded by 10.1)
- Windows Server (no year specified).
The first two claims are correct. Main website is behind Cloudflare, self-hosted BTCPay instance is behind MAXKO Hosting, mentioned earlier in post #24. Here are their requirements:
- Email address
- JavaScript
Also has a self-hosted BTCPay instance with their own Onion-Location, supports Monero only. Main website does not have an Onion-Location, and also has similar obsolete Linux distribution issues.
To expand on my previous concerns…
- List of Hosting Providers That Accept Cryptocurrencies or Cash as Payment - #8 by Patrick
- List of Hosting Providers That Accept Cryptocurrencies or Cash as Payment - #11 by Patrick
- Abolishing Third Party Hosting Services in wiki
A new account seems to have been created for the purpose of advertising its service in the list of providers that accept privacy-friendly payment methods.
Note: I do not know anything about the service where this first happened. It might be completely fine, or not. I do not want to even look into that for the purpose of this post.
I was not sure whether we want to allow that kind of advertising, but given that the entire purpose of the thread is finding providers like this, it might be weird to block it.
From a threat model standpoint, arguably a provider that allows anonymous payment does not necessarily have to be trusted, so long as no one puts anything deanonymizing or sensitive on the server?
But lots of people put sensitive things on servers. For instance, onion service private keys necessarily need to be on the server. What if the server provider is allegedly snooping on user data? It is not a good use of project time to investigate and adjudicate that.
Can data snooping by server providers be prevented technically?
- In theory, yes, with Confidential Computing.
- In practice, probably not. No user has documented reproducible steps for such a setup yet.
At this time, the customer has to trust the hosting provider.
Attack methodology.
- create a malicious service that accepts anonymous payment
- advertise it
- get it into the list of hosting providers
- users start using it
- snoop/manipulate user data
For this reason…
…it’s best for Whonix to stay out of hosting this list.