I was wondering there was a way to keep it(i2pbrowser) out of /usr/bin if i2p wasn’t installed yet, but put it back into /usr/bin if i2p were installed later. It was just a thought I had since @nurmagoz and @goldstein-otg both noted that /usr/bin/i2pbrowser was installed by tb-starter automatically when using stretch-testing.
Not easy. Would require /usr/bin/i2pbrowser in separate package. Maybe not worth it. Perhaps you could do that in case you invent a workstation package anyhow.
Can we get all from packages.debian.org? If so, I am wondering if we install all by default one day.
@goldstein-otg there is a problem with I2P to respond with command lines orders , as it will not reflect them to effect its GUI.
e.g: turning off the outproxy with cli command , it doesnt change the gui.
so until I2P fix that , we need to have either double changes gui&cli or we have own whonix-gw-i2p to include git changes and we make it as a persistent preinstalled configurations.
i have checked the router console and outproxies are disabled at my end.
whonix-i2p-setup(WIP) is going to take care of the needed changes, there is nothing for I2P to fix except a .d style config maybe.
Even if the Router would ignore our Outproxy changes there would be no outproxy traffic because privoxy is blocking it.
just wanted to clearify that even TBB in whonix doesnt has the same feature of normal TBB working in plain Debian. As per tab connection isolation feature its not working inside TBB in the workstation (yet).
So TBB whether with Tor or with I2P acting the same inside whonix until one of them got fixed to produce per tab isolation.
there is a problem i have discovered in the router , that it change itself to SHA-1 (insecure) sometimes which is sucks and the I2P team leaving that option in order to not loose the old routers connection/speed. I see it as a bullshit idea and i hope if we can remove that in the router and provide only the latest encryption which is Ed25519-SHA-512.
There is good news as well , a contributer (might later follow up) called Dr|Z3D hes a java/css developer and he forked the original I2P and made his modifications and called it I2P+. I talked to him about whonix-i2p and hes willing to help but i told him that he needs to work integrating I2P+ into Debian otherwise it will not be secure to just download the modifications and merge them with the original I2P and hes studying that …
he owns Skank which has good track of I2P sources: http://skank.i2p/
and this is his I2P+ work: skank.i2p/static/i2p+.html
This is rubbish. Stream isolation is there and you can test for yourself. We don’t modify Tor Browser in any major way from upstream.
Apologies , disculpas , 謝罪 …
it was my mistake , i thought since Tor in the GW torifing everything then tab tab tab wont produce another connection.
but i think patrick done pretty well job to make it happen.
Edit by Patrick:
gif removed one disabled upload of gif
Issues Related/Useful To be Solved for Whonix-i2p
- eche|on (one of I2P members) said I2P doesnt give the same path for 2 different websites request:
<anonymousmaybe> but if alice talking to bob + zzz + i2pwebsite on the same time at the same browser
<anonymousmaybe> will each of them has its own tunnelings ?
<anonymousmaybe> alice -> A -> B -> C -- D -> E -> F -> bob
<anonymousmaybe> alice -> X -> Y -> Z -- L -> M - > N -> zzz
<anonymousmaybe> zzz & bob opened at the same time in the browser
<anonymousmaybe> if thats the scenario happening at I2P now its just great
<anonymousmaybe> if not , then correlation per different connections is very possible
<eche|on> anonymousmaybe: you need to devide into in/out tunnels
<eche|on> and different services do have different IN tunnels, if they have the same IN tunnel, it is the same server
<anonymousmaybe> yeah as a client/user i care about the outbound
<eche|on> it could also be alice - a - b- c- l -m- n - zzz
<eche|on> but never alice -> X -> Y -> Z -- L -> M - > N -> bob AND alice -> X -> Y -> Z -- L -> M - > N -> zzz
<anonymousmaybe> thats cool then
- I2Pmail should be avoided for anonymous usage:
- Splitting I2P router from its services is possible but it will take long time
https://trac.i2p2.de/ticket/2132
- reseeding through Tor/Socks5 seems to be not working
https://trac.i2p2.de/ticket/2342
- I2P router makes multiple requests through outproxy while its disabled
https://trac.i2p2.de/ticket/2338
- configuring i2p with dpkg autostart doesnt work
https://trac.i2p2.de/ticket/2323
- i2prouter doesnt recognize I2P running within Systemctl
https://trac.i2p2.de/ticket/2324
- CLI commands doesnt has GUI effects
https://trac.i2p2.de/ticket/2335
- Running I2P as root is not solvable (though recommended against)
https://trac.i2p2.de/ticket/2336
- Add optional to remove completely “I2P News”
I don’t see a problem here, most points are not really an Issue and are going to get resolved by postman. It should be used like every other clearnet mail…
Right, i talked to the Devs about that a couple of months ago, it’s on their list.
Like Slumlord already commented, i can’t reproduce this issue… nothing to fix here
Yes, i mentioned this already, not an issue for us, we use a custom startup script (soon™)
We don’t need/use the i2prouter script, so no issue for us
Can’t reproduce this, works for me. Like ZZZ replied this should not happen.
Not an Issue for Whonix-I2P, but noted.
Don’t know about this, seems to be a minor issue…
Thanks for sharing these
Well no its not gonna be fixed by postman, i spooked to him and said he dont have time to do any of them but if there is someone willing to do it he can take the lead.
slumlord?
True , but since it should be working by default then its better to have it fixed by default (in case our scripts failed , there is a workaround)
Happening with me , dunno lets see once you finish Whonix-I2P i will give it another shot.
Anytime ![]()
Well this sucks, i guess we have to wait for someone to fix it then.
He commented on the ticket Sign in · GitLab
We replace/remove this script to avoid these issues, otherwise it’s going to confuse users because of the different config & dir.
Working on it ![]()
Have you tried to use the Outproxy ? Does it work or is it just a bug in the GUI ?
Privoxy should block clearnet links anyway, but i’m going to see if i can reproduce this bug.
I’m trying to get the Whonix-I2P-Setup Package up and running until the next holidays (no promise though)
lets see when i test the new version of Whonix-I2P and check if thats going to happen or not. (or if can test Tor while using bridges like obfs4)
oh i see
i disabled the outproxy from the tunnel itself by removing fals.i2p and meeh somthing links.
sure np tyt (but not too much ![]() )
)
Strictly speaking, I don’t think it has the same path, just the same return address. I was curious and technically the fingerprinter is partly broken(by browser improvements mostly) for the moment, but the destination that the server sees(to reply to the HTTP proxy tunnel) is still the same across the sites you visit. I linked to some pics at the the bottom. It’s arguably not that much of an issue. The destination expires automatically and is arguably of fairly limited utility. It doesn’t de-obfuscate your location and it can’t really lead to cross-site identification in and of itself, it needs to be combined with another identifiable characteristic that lives longer like a user account or possibly, a browser fingerprint. I just think that it could be less useful if each site got a different tunnel to reply to.
Also this guide is available now Whonix i2p Browser Vanilla Debian Tutorial, not strictly Whonix related but it does use this configuration.
excellent , thx alot for that study.
although it shouldnt be through TBB only , if its possible for you can you compare the results of a clearnet browser like Firefox or any garbage browser like chrome or IE?
because when you do the test , it should benefit what I2P recommending now as they telling in their instructions to use those browsers. not just what you recommending to use (modified TBB).
I actually wrote that documentation under their instruction, the browser recommendation is in the process of being updated, that is likely to comprise part of it. I’ve got a couple important things to squeeze into that process this week, hope to make some serious headway tomorrow.
I’ve got to finish a couple things with the fingerprinter, I kind of left it off mid-feature and need to fix it but work has been very busy, but once I fix it I will be continuously doing this and updating the fingerprint screenshot for at least a handful of browsers in default and modified configurations. I have tried it with a hardened non-tor Firefox already using this GitHub - eyedeekay/firefox.profile.i2p: Importable Firefox profile for use with i2p. Also usable with Tor Browser on most platforms., but now that I’ve actually run a current Tor Browser on a Windows machine and know it has a path I can fetch with an environment variable, that may change to Tor Browser as well pending some discussion. There was some friction shipping an alternate Firefox profile at first. I’ll also be doing probably at least vanilla Firefox, Vanilla Chrome, and either ungoogled-chromium or Brave as well.
On another topic, if we want out-of-router i2p applications, neither disabling the default ones nor writing new ones is terribly difficult. I’ve got a considerable amount of time in it already actually.
cd "$HOME/.i2pb/i2p-browser/Browser/" || exit 1
Non-ideal since in failure case would exit 1 without error message.
Is this even required? If that was to fail, it would be handled by proper error handling by /usr/bin/torbrowser anyhow? Could you remove please and test?
I think you’re right, and I think that this might be better link to diff. The top one is actually essential because in the non-presence of the browser it will still attempt to copy all those files into the non-existent folders.
No connection to irc what so ever:
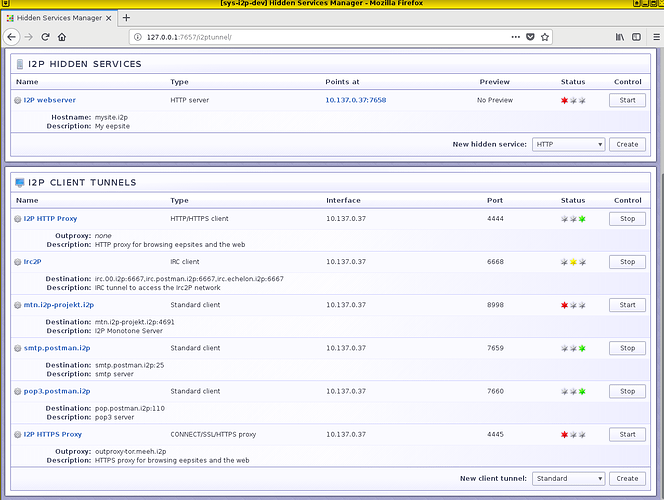
For IRC over i2p, the following seems to work:
- Open HexChat
- server/port := 127.0.0.1/6668
- Disable proxy server:
Settings > Preferences > Network Setup > Proxy Server > Type = (Disabled)
yes true , but it needs to be disabled by default in Whonix-I2P-Template (when there will be separated builds)